SaferWEP (2003)
Around the time I wrote Poindexter I was experimenting with WEP password cracking. WPA wasn’t avaiable around this time and sadly 40-bit WEP keys were still very common and trivial to break. I discovered a Java library that could configure early Airport base stations and I was off and running. SaferWEP improved the security of a WEP network by rotating a weak WEP key faster than it could be cracked. Clients ran a time-based secret generator similar to Google Authenticator.
From the README:
This package is an attempt to improve the security of airport based WiFi
networks. It consists of two jar files: a "master" and a "client". A Java-Cocoa
app is also included for mac clients because it should load faster than the
client jar file. The function of the master program is to set the WEP key on the
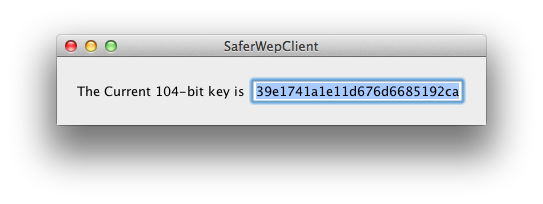
base station. The client is a simple GUI that displays the current key for the
WiFi network.
The key is currently generated by taking a shared password and computing a SHA1
hash of the password with the current system date. The current scheme generates
keys that are good for only the current day based on my naive assumption that it
would take longer than a day of sniffing to get a 104-bit WEP key. If this is a
silly assumption then the software should be modified to allow for creating keys
based on the hour of the day as well.
CURRENT KEY CREATION METHOD
sharedSecret = "thePassword"
currentDate = "2003-8-28"
sha1(sharedSecret + currentDate) = ca7e452415af92df50ebb4d0d8d59b5817b41a00
The 104-bit key would be ca7e452415af92df50ebb4d0d8
The 40-bit key would be ca7e452415af9
I announced SaferWep in August of 2003 but didn’t work on it too much more after that.